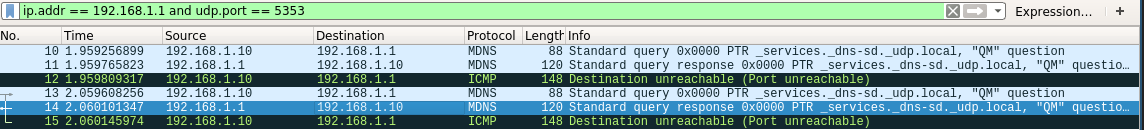
UDP Flood attack not interrupted and the two communicating hosts' will... | Download Scientific Diagram

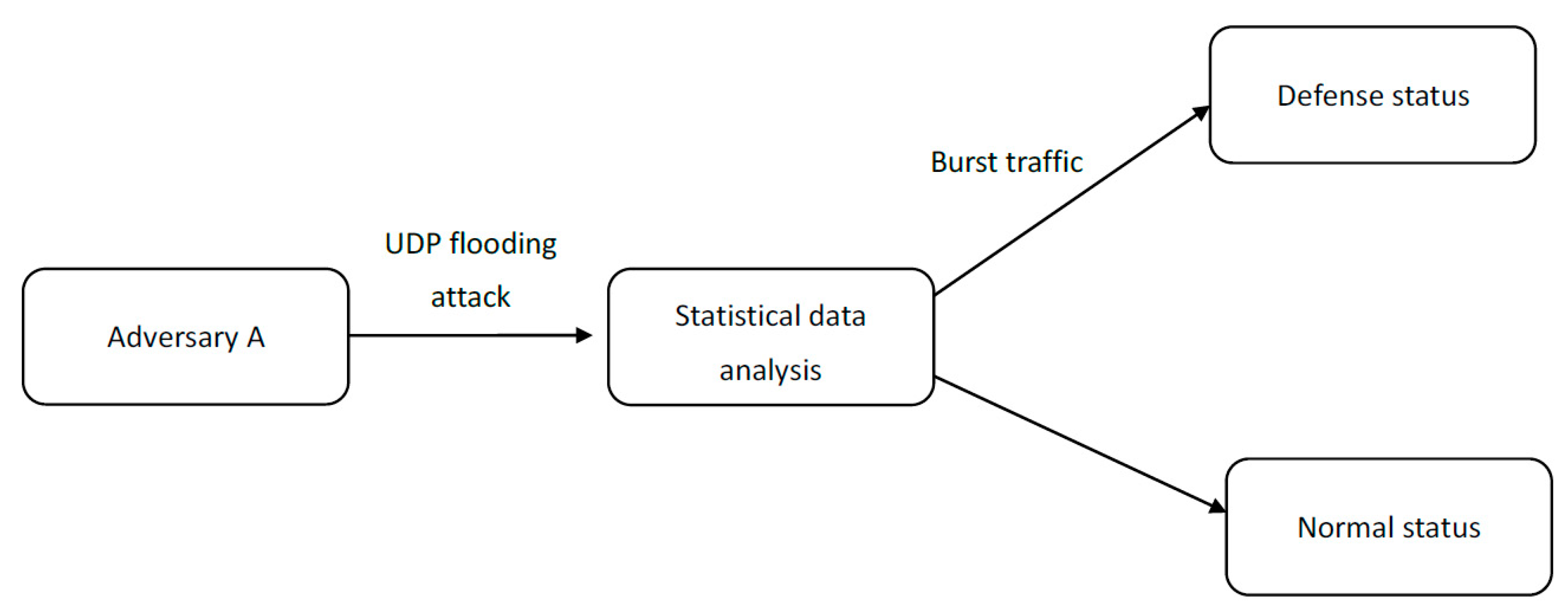
Basic UDP Flood Attack. DDOS and Anti-DDOS methods. Articole introductive si ajutor | Evidweb Network
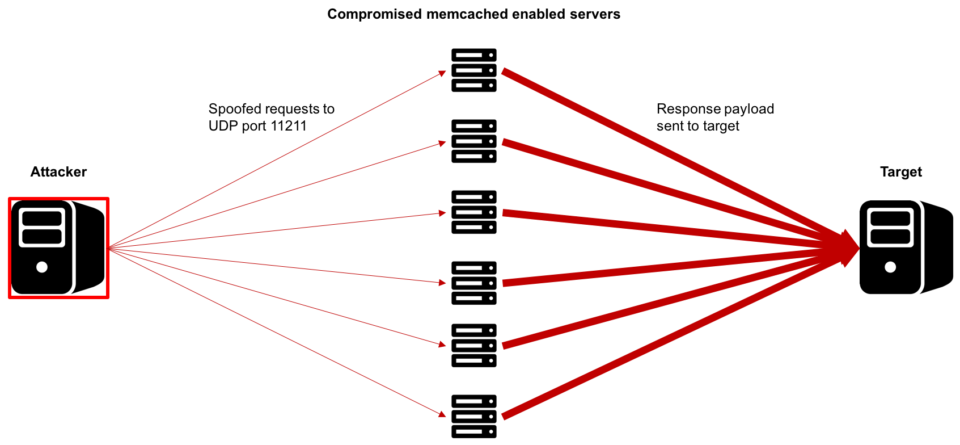
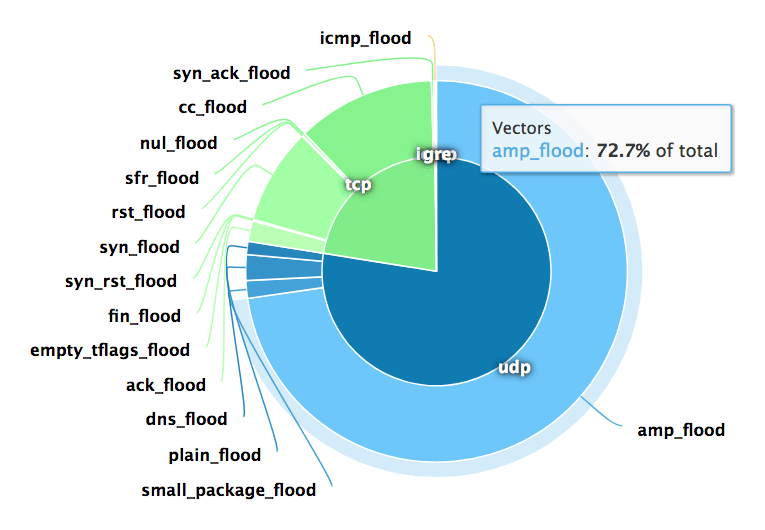
Use Dome9 to Prevent Memcached-based DDoS Attacks from Your Cloud Environment - Check Point Software